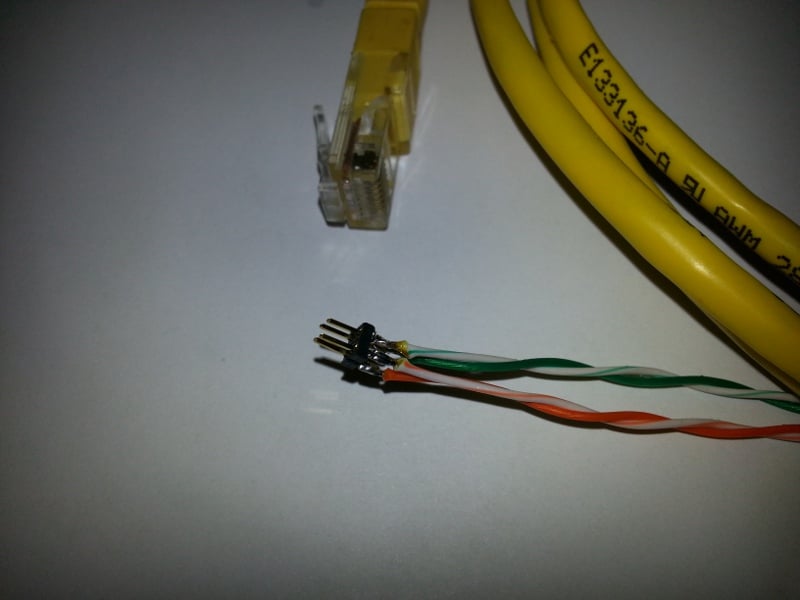
Almost everyone knows that there is a white 4 pin connector on the left of the dashboard :smile:
Today I susscefully connected to this connector, with a 2 row 4 contact male header (2mm pitch)
The ethernet network of the car contains 3 peripherals :
- The center console, IP Address 192.168.90.100
- The dashboard/navigation screen, IP Address 192.168.90.101
- An unknown peripheral, IP Address 192.168.90.102
These 3 peripheral send of lot of data in broadcast UDP, to 192.168.90.255 broadcat address. Different UDP ports are used depending of data type.
In fact they use the same principle a CAN bus use :
- Everyone send data on the network
- Anyone who need it listen for this data.
The data shared on the netword seem to be in clear. I can see a Ascii header which define the type of the frame. Some data are in binary format thus it will need some reverse engineering to understand the data.
I also tested the openeds ports of the 3 peripherals :
- Central console :
PORT STATE SERVICE
22/tcp open ssh
53/tcp open domain
80/tcp open http
111/tcp open rpcbind
2049/tcp open nfs
6000/tcp open X11
MAC Address: FA:9E:70:EA:xx:xx (Unknown)
- Dashboard screen :
PORT STATE SERVICE
22/tcp open ssh
111/tcp open rpcbind
6000/tcp open X11
MAC Address: 36:C4:1F:2A:xx:xx (Unknown)
- Unknown device :
PORT STATE SERVICE
23/tcp open telnet
1050/tcp open java-or-OTGfileshare
MAC Address: 00:00:A7:01:xx:xx (Network Computing Devices)
Today I susscefully connected to this connector, with a 2 row 4 contact male header (2mm pitch)
The ethernet network of the car contains 3 peripherals :
- The center console, IP Address 192.168.90.100
- The dashboard/navigation screen, IP Address 192.168.90.101
- An unknown peripheral, IP Address 192.168.90.102
These 3 peripheral send of lot of data in broadcast UDP, to 192.168.90.255 broadcat address. Different UDP ports are used depending of data type.
In fact they use the same principle a CAN bus use :
- Everyone send data on the network
- Anyone who need it listen for this data.
The data shared on the netword seem to be in clear. I can see a Ascii header which define the type of the frame. Some data are in binary format thus it will need some reverse engineering to understand the data.
I also tested the openeds ports of the 3 peripherals :
- Central console :
PORT STATE SERVICE
22/tcp open ssh
53/tcp open domain
80/tcp open http
111/tcp open rpcbind
2049/tcp open nfs
6000/tcp open X11
MAC Address: FA:9E:70:EA:xx:xx (Unknown)
- Dashboard screen :
PORT STATE SERVICE
22/tcp open ssh
111/tcp open rpcbind
6000/tcp open X11
MAC Address: 36:C4:1F:2A:xx:xx (Unknown)
- Unknown device :
PORT STATE SERVICE
23/tcp open telnet
1050/tcp open java-or-OTGfileshare
MAC Address: 00:00:A7:01:xx:xx (Network Computing Devices)